Pentagon officials are currently scrambling to verify claims from an Iran-linked hacking group that has reportedly published the personal details of 2,379 US Marines. While the headlines focus on the number of troops, the real danger lies in how this data is being used: as a psychological weapon delivered directly to the pockets of service members through WhatsApp.
This isn't just another corporate data breach where you change your password and move on. The group responsible, known as Handala, isn't just dumping spreadsheets on the dark web. They’re reportedly sending targeted threats to Marines stationed in Bahrain and across West Asia, claiming to know their home addresses, their daily routines, and even the names of their family members. Read more on a related topic: this related article.
The Handala Hack and Why It Hits Different
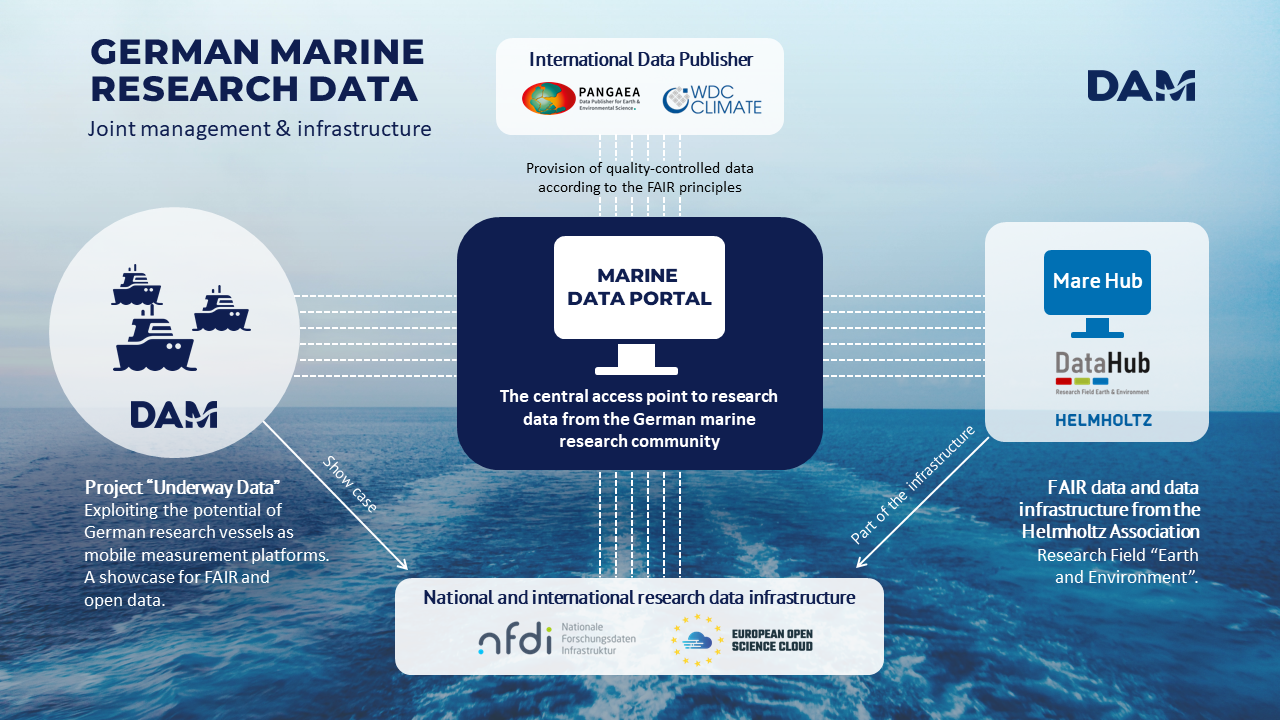
Handala isn't a new name in the world of state-sponsored cyber warfare, but their tactics have turned significantly more aggressive. Early reports suggest the leaked data includes names, ranks, and contact information for Marines deployed in the Persian Gulf. By publishing this on a Telegram channel, the group isn't just trying to steal secrets; they're trying to erode the sense of security that service members and their families rely on.
The timing of this "hack-and-leak" operation is far from accidental. It comes at a moment of extreme tension, with a US naval blockade choking Iranian oil revenue and the Strait of Hormuz becoming a literal flashpoint. When a hacker sends a WhatsApp message to a young Marine telling them they're being watched by "Shahed drones," they aren't necessarily looking for a technical win. They’re looking to get inside that Marine’s head. Additional analysis by The New York Times delves into related perspectives on this issue.
Verification and the Pentagon’s Response
It’s easy for a hacking group to claim they’ve compromised thousands of files. It’s much harder to prove it. However, the Wall Street Journal has reported that preliminary Pentagon findings suggest at least some of the leaked data is authentic. This confirms a breach occurred, though the exact source—whether it was a government server, a third-party contractor, or a compromised administrative tool like Microsoft Intune—is still being investigated.
You’ve got to look at the broader context of Iranian cyber operations in 2026. This isn't an isolated incident. Just weeks ago, groups linked to Iran’s Ministry of Intelligence and Security (MOIS) were caught targeting critical infrastructure, specifically programmable logic controllers (PLCs) in US water and energy sectors. They aren't just looking for emails anymore; they're looking for physical leverage.
What the leaked data actually contains
- Full names and ranks of over 2,300 active-duty personnel.
- Physical home addresses and family links.
- Daily movement patterns and surveillance-based routines.
- Direct contact information used for targeted harassment.
Why Personal Data Is the New Front Line
We often think of cyber warfare as "The Matrix" style code-breaking against a high-tech fortress. The reality is much grittier. Most of these breaches start with something boring: a spear-phishing email to a contractor or an unpatched vulnerability in a piece of software from 2021.
Handala’s strategy of "information operations" is designed to create a "state of collapse" in morale. By threatening the families of troops, they bypass the military’s high-tech defenses and strike at the individual's psychological well-being. This is a classic "false-flag" and "hack-and-leak" hybrid. They use the data to back up their threats, making the service member believe the enemy is behind every corner.
The Trump-Iran Connection in 2026
Adding a layer of bizarre complexity to this situation, President Trump recently posted on Truth Social that Iran is in a "State of Collapse" and is begging for the US to open the Strait of Hormuz. While the hackers are projecting strength through data leaks, the official diplomatic narrative suggests a country under immense pressure.
Is the leak a show of strength from a regime that's actually falling apart? Or is it a desperate move to gain leverage in a negotiation that isn't going their way? Either way, the 2,379 Marines whose names are now in the public domain are the ones paying the price for this digital tug-of-war.
Moving Beyond Simple Passwords
If you’re a service member or work in the defense sector, the old advice of "don't click on links" isn't enough. The Pentagon is likely going to enforce even stricter hardware-based authentication (like Yubikeys) and move away from any reliance on mobile-based MFA which can be intercepted or bypassed.
The immediate next steps aren't just for the generals in the Pentagon. Service members need to scrub their digital footprints. This means tightening privacy settings on social media, using encrypted messaging apps that don't reveal phone numbers, and being hyper-aware of "doxing" risks. If your data is already out there, the focus shifts from prevention to mitigation—changing phone numbers, alerting family members to potential phishing attempts, and reporting any unsolicited contact to command immediately.
The days of assuming your military service is a private matter are over. In 2026, your digital identity is as much a target as the base you're stationed on.